Effectively Addressing Cyber Attacks and Insider Threats
Cyberattacks are becoming increasingly stealthy, targeted, and constantly evolving. Enterprises must continuously assess their security risk posture, promptly upgrade security protection systems, and optimize incident response and recovery processes to address the ever-changing threat landscape. According to the latest 2025 Verizon DBIR (Data Breach Investigations Report), the vast majority of security incidents originate from the following causes or initial attack vectors:
Key Findings
- Credential Abuse is the most common initial intrusion vector
Approximately 22% of confirmed breaches show that stolen or leaked credentials were used as the attacker’s entry point. - Vulnerability Exploitation has rapidly risen as a major entry path
Exploitation of vulnerabilities in systems or perimeter devices (such as VPNs and edge devices) accounts for about 20% of breaches. This represents a significant increase of 34% compared to the previous year. - Phishing and social engineering / human factors remain highly significant
Phishing is another major entry vector, accounting for approximately 16% of breaches, and is often a critical link in the attack chain for human-driven or social engineering incidents. Human factors (such as clicking malicious links, being deceived, or configuration errors) are involved in roughly 60% of breaches. - Third-party involvement has increased significantly
Compared to the previous year, breaches involving third parties have doubled, rising from about 15% to 30%. This includes compromised software supply chains, weak security controls at service providers, and leaked credentials from partners.
Overall, the majority of security breaches are caused by stolen/leaked credentials, unpatched or exploited vulnerabilities, and phishing/social engineering driven by human factors. These initial access vectors collectively form the primary attack paths, with credential abuse remaining the most dominant source.
Response Strategy
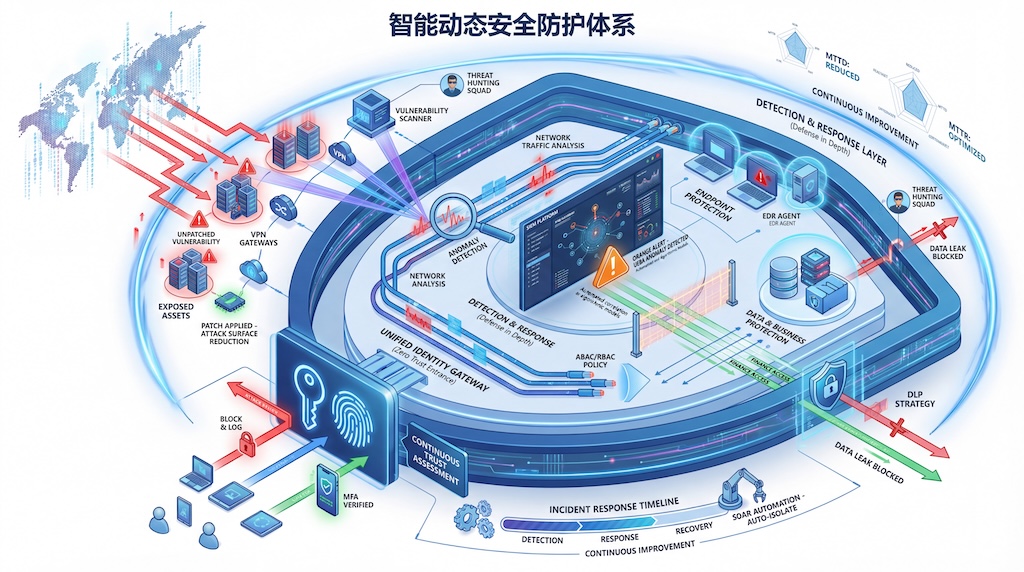
I. Overall Approach: Zero Trust Combined with Defense in Depth
- Zero Trust: No user or device is trusted by default; all access must be continuously verified.
- Defense in Depth: Layered protections across networks, applications, data, and endpoints to avoid single points of failure.
II. Prevention
1. Account and Identity Security
- Multi-Factor Authentication (MFA): Mandatory MFA for all high-sensitivity systems and remote access.
- Least Privilege Access Control: Strictly limit permissions using role-based and attribute-based access control (RBAC/ABAC).
- Secrets Management: Use centralized credential vaults with automated rotation to prevent long-term credential exposure.
2. Vulnerability and Patch Management
- Automated Vulnerability Scanning: Regularly scan operating systems, applications, and perimeter devices.
- Patch Prioritization Strategy: Prioritize remediation based on CVSS scores combined with business risk.
3. Phishing and Social Engineering Defense
- Email and Web Security Gateways: Detect and block phishing emails and malicious links.
- Security Awareness Training: Conduct regular phishing simulations to help employees recognize social engineering attacks.
4. Data and Endpoint Protection
- Endpoint Detection and Response (EDR): Deploy behavior-based detection and protection agents on all endpoints.
- Data Loss Prevention (DLP): Monitor the movement of sensitive data during transmission, storage, and usage.
III. Detection
- Security Information and Event Management (SIEM): Centralized log collection and correlation analysis to identify anomalous behavior.
- Network Traffic Analysis (NTA) and Threat Intelligence: Detect lateral movement and malicious command-and-control (C2) traffic.
- User and Entity Behavior Analytics (UEBA): Identify abnormal internal user behavior and potential insider threats.
IV. Response
- Security Orchestration, Automation, and Response (SOAR): Automate isolation, blocking, and notification for confirmed attacks.
- Incident Response Plans and Drills: Conduct regular tabletop exercises and red-blue team simulations to ensure team readiness.
- Forensics and Root Cause Analysis: Ensure logs, traffic data, and endpoint images are traceable after incidents occur.
V. Continuous Improvement
- Attack Surface Management (ASM): Continuously discover and reduce internet-exposed assets.
- Threat Hunting: Proactively search for hidden or persistent threats within the environment.
- Security Metrics and Assessment: Regularly measure metrics such as MTTD (Mean Time to Detect), MTTR (Mean Time to Respond), and data breach exposure risk.
VI. Layered Strategy Matrix
| Protection Layer | Technologies & Methods | Primary Objective |
|---|---|---|
| Identity & Access | MFA, RBAC/ABAC, Zero Trust Architecture | Prevent credential abuse |
| Network & Perimeter | Network segmentation, micro-segmentation, NTA, IPS | Block lateral movement |
| Endpoints & Applications | EDR, patch management, application whitelisting | Defend against malware and exploits |
| Data & Storage | DLP, encryption, backup and recovery | Protect sensitive data, reduce leak risk |
| Detection & Response | SIEM, SOAR, UEBA, threat hunting | Rapid detection and response |
| People & Processes | Security awareness training, red-blue exercises, tabletop drills | Reduce human error and improve response capability |
What PolarSight Can Provide
The PolarSight Security Services Team, based on the PolarSight Threat Management Framework, delivers comprehensive security solutions and professional services to help enterprises:
- Protect critical applications and digital assets
- Achieve effective data governance and risk management
- Meet a wide range of compliance and regulatory requirements
